NTLM is going away: what Microsoft’s phaseout means for MSPs and IT teams
Why legacy authentication is a growing security risk—and how to prepare for a Kerberos‑first Windows environment
Takeaways
- NTLM is a known security risk that enables techniques commonly used in ransomware and other attacks.
- Deprecation is already underway, and future Windows releases will disable NTLM by default unless explicitly re‑enabled.
- Identifying hidden NTLM dependencies and validating Kerberos compatibility are critical for a successful migration.
Microsoft is slowly phasing out its long-standing authentication protocol, NT LAN Manager, or NTLM. This is one of those legacy technologies that has worked ‘well-enough’ for decades, since the first version was introduced in 1993 with Windows NT 3.1. Microsoft rolled out NTLMv2 six years later in Windows NT 4.0 Service Pack 4.
At the time of its release, NTLM solved a big problem for business networks. Companies were still using single-user desktops and simple workgroups to domain-based networks with centralized authentication and file sharing. Among other features, NTLM provided challenge-response authentication and stronger hashing, which was a huge improvement over its predecessor. It worked great for what it was meant to do, but it was never meant to secure identities from the threats we see today. Threats like pass-the-hash, credential relay and lateral movement are enabled by the limitations of NTLM.
If you’re wondering why NTLM is still around after 30 years, the answer is simple. NTLM is very forgiving. Broken DNS? Unsynchronized clocks? Legacy applications? NTLM authentication works in these scenarios, where Kerberos and other modern mechanisms will not. Even hardened networks may be using NTLM as a ‘fallback’ method for some systems.
What is Microsoft doing?
Microsoft first announced the deprecation of NTLM in 2023 and formally deprecated the protocol in mid-2024. Three distinct phases have been defined to help managed service providers (MSPs) and IT teams move away from NTLM toward Kerberos:
Phase 1 (Current): Microsoft rolls out enhanced auditing tools to give admins visibility into where NTLM is still lurking. Microsoft has details on the auditing enhancements here.
Phase 2 (Late 2026): Initial and Pass-Through Authentication Using Kerberos (IAKerb) and local Key Distribution Center (KDC) will be added to Windows systems. These will help eliminate the need to use NTLM as a fallback mechanism. Get more information on these features in this Microsoft article.
Phase 3 (Future): NTLM will be disabled by default in next-generation Windows releases, requiring explicit policy overrides to re-enable.
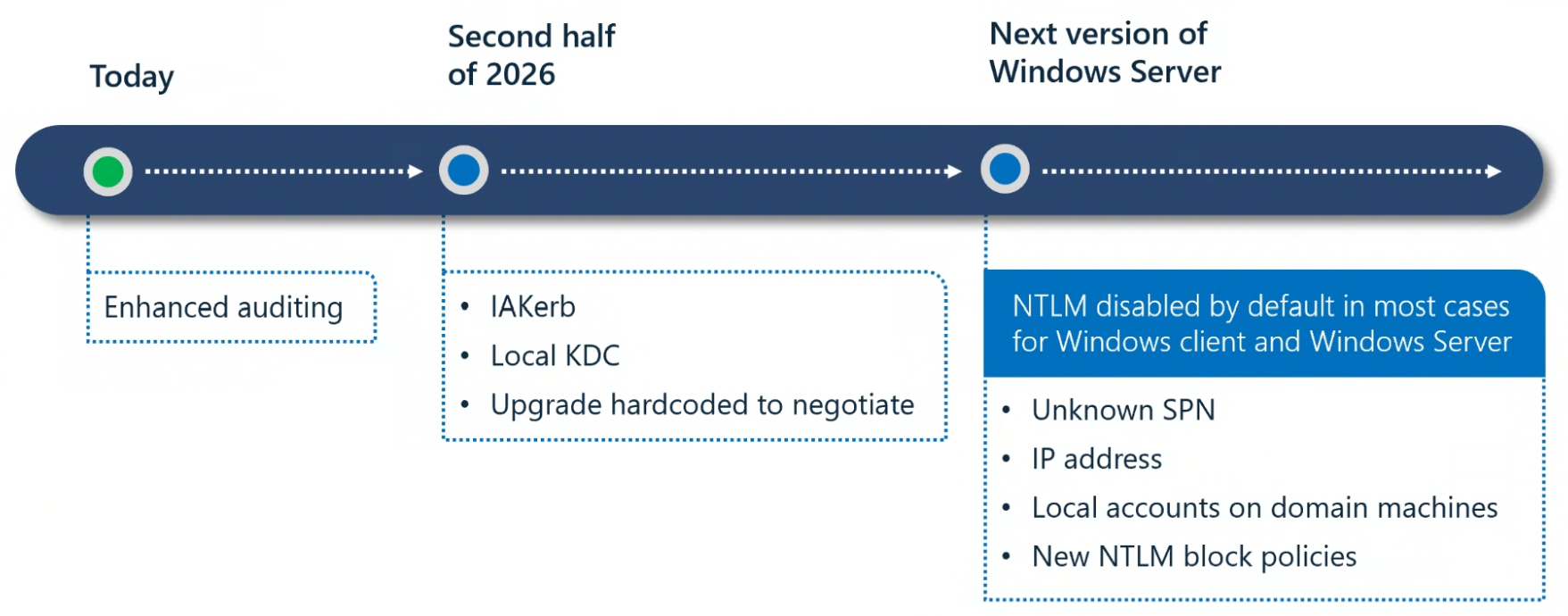
Microsoft roadmap of a three-phased approach of transition away from NTLM, via Microsoft
This migration represents a massive shift in security for Windows systems and could come with some challenges and costs. Legacy systems, hardcoded authentication, embedded systems like HVAC controllers, and hidden ‘fallback’ configurations can take time to identify and fix.
What’s involved in migration?
Before NTLM can be disabled, MSPs and IT teams must first identify where it is being used. This is investigative work that is supported by the new enhanced auditing features. The process may be time-consuming, especially if NTLM is only used during specific times or events.
Anything using NTLM must be tested with NTLM disabled. This can involve setting up the test environments, configuring Kerberos authentication and working with end-users to validate functionality.
When everything has been tested, migration from NTLM to Kerberos could be handled through a group policy or it could require upgrades or code changes. MSPs and IT teams may need to coordinate with multiple vendors and support teams. There may be unexpected delays that extend the timeline of the project.
Just like any other IT project, there should be a period of monitoring and communication to identify and address any unexpected effects on users. This is a good time to document new procedures or policies and train anyone who may need to address issues as they arise.
Ongoing monitoring after the project will help ensure that NTLM is not reintroduced into the network.
NTLM is a security risk
NTLM is exploited by dozens of threat groups like Volt Typhoon, Scattered Spider, Wizard Spider and Dragonfly. The hash-based authentication model is a root enabler for attacks that lead to ransomware or advanced persistent threat (APT) intrusions. Still, Microsoft continues to find the use of NTLM “prevalent in enterprise environments where modern protocols like Kerberos cannot be implemented due to legacy dependencies, network limitations, or ingrained application logic.” Hopefully these organizations are actively working to eliminate NTLM dependencies.
Companies may not want to invest in an NTLM project, especially if they have just invested in a bunch of new Windows 11 machines. It can also be tough to explain NTLM to a non-technical audience. Still, NTLM is a business risk and business leaders usually do understand the impacts of a ransomware attack. Moving to Kerberos authentication is a strategic security investment with long-term benefits, and it should be done as soon as possible.

Rapporto sulle violazioni della sicurezza e-mail 2025
Risultati chiave sull'esperienza e l'impatto delle violazioni della sicurezza e-mail sulle organizzazioni a livello mondiale
Iscriviti al blog di Barracuda.
Iscriviti per ricevere i Threat Spotlight, commenti del settore e altro ancora.
The MSP Customer Insight Report 2025
Uno sguardo globale su ciò di cui le organizzazioni hanno bisogno e vogliono dai loro provider di servizi gestiti per la sicurezza informatica





