Sandworm: Russia's global infrastructure wrecking crew
Inside APT44: how GRU Unit 74455 blends cyber sabotage, strategic access, and physical-world disruption
Key takeaways
- Sandworm (APT44) is a GRU‑backed threat actor responsible for landmark attacks such as the 2015 Ukrainian power outages and the 2017 NotPetya attack, demonstrating unmatched capability in cyber‑enabled physical disruption
- The group prioritizes destructive operations over financial gain, using wipers, ransomware‑style malware, and edge device exploitation to degrade critical infrastructure and create widespread operational impact
- Defending against Sandworm requires layered security focused on edge hardening, phishing‑resistant identity controls, IT/OT segmentation, and recovery planning for destructive attacks
Sandworm is a threat group attributed to the Russian Federation (Russia) General Staff Main Intelligence Directorate (GRU). The group operates as a unit within the Russian military and was identified in 2014 while using BlackEnergy malware and a Windows zero‑day (CVE‑2014‑4114) to conduct spear phishing and reconnaissance operations. It wasn’t until December of the following year that the group showed how truly dangerous it was at the time.
Here’s your quick look at Sandworm:
Threat type |
State-sponsored advanced persistent threat (APT) conducting sabotage, espionage and influence operations as a unit within Russia's GRU. |
Unique trait |
The only threat actor to have successfully caused malware-induced power grid blackouts. |
Targets |
Critical infrastructure, government organizations, defense industrial base, international institutions. The group targets Ukraine and NATO member states and runs opportunistic attacks which have impacted dozens of non-targeted countries. |
Initial access |
Exploitation of web applications, network edge devices, routers and mail servers. Spear phishing and trojanized software are also favorites. |
Extortion method |
None — Sandworm is not a ransomware operator, though it will use ransomware as a pretense to confuse victims and defenders. |
Leak site |
Sandworm has no leak site, but coordinates with hacktivist front groups to execute strategic data leaks and provide the GRU with plausible deniability. |
Sandworm may use a military emblem or some other official insignia as part of the GRU, but it has no public-facing logo or brand. Instead we’ll look at Sandworm’s place within the organizational structure of the Russian intelligence apparatus. The following diagram was published by the United Kingdom (UK) Foreign, Commonwealth & Development Office in 2023 and is based on intelligence gathered by UK investigators. You can view a larger image here.
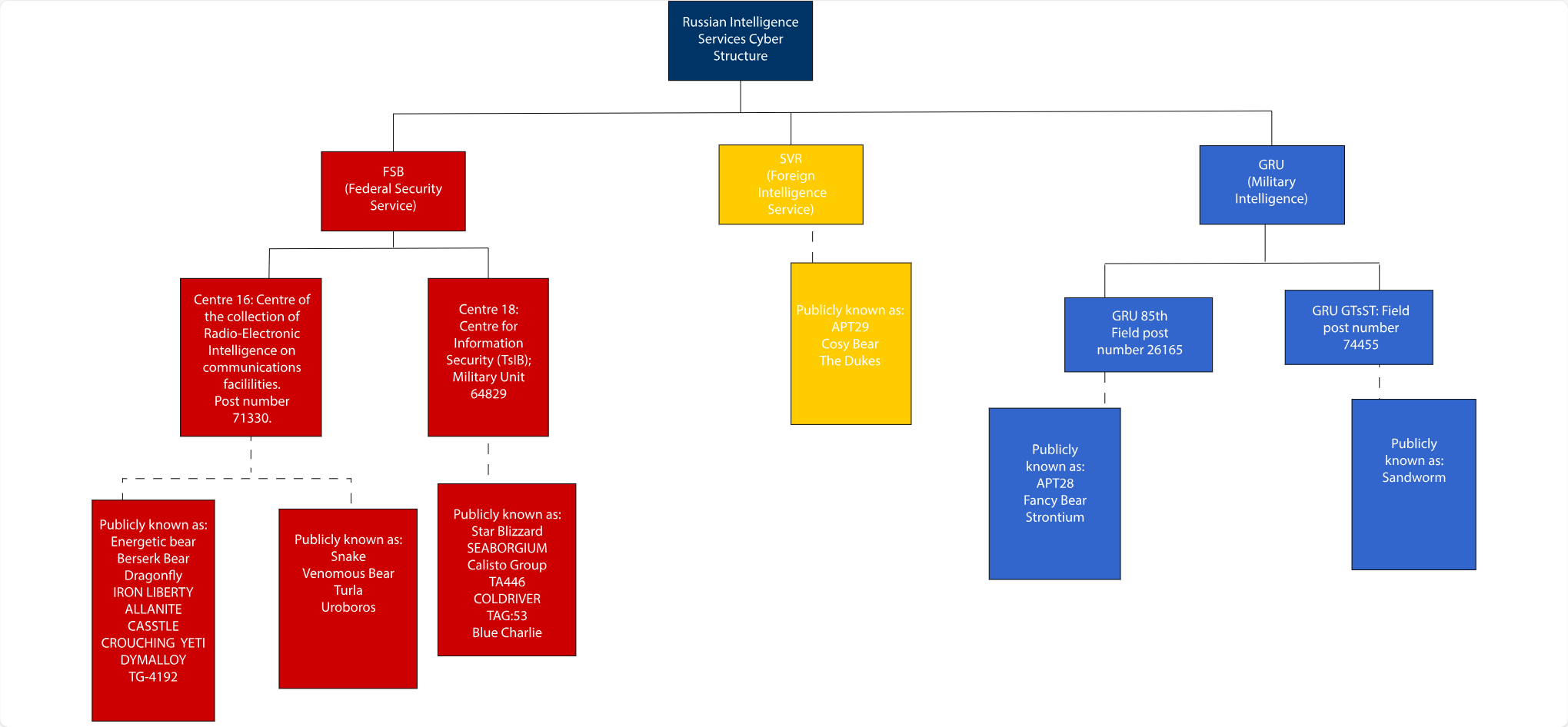
Russian Intelligence Services cyber organogram
You will see the Sandworm group in the lower right of the diagram, reporting to the GRU. The other two agencies at the GRU level are the Federal Security Service (FSB) and Foreign Intelligence Service (SVR). These three agencies have different missions and tactics:
- FSB: The direct successor to the Soviet Union KGB. This agency handles domestic security, counterintelligence and border patrol. Subunit Center 16 focuses on intercepting communications, decrypting messages and penetrating foreign networks. Center 18 carries out espionage missions via spear phishing and data exfiltration. Multiple threats have been attributed to each of these subunits.
- SVR: This agency conducts classic foreign espionage. Targets include governments, think tanks, research organizations, and any company that may have strategically important information or assets. The SVR prioritizes long-term access over destruction and is known to target cloud resources and supply chains. APT29 / Cozy Bear is believed to operate within the SVR.
- GRU: The focus here is military intelligence with an emphasis on cyberwarfare and sabotage. Subunit GRU 85th specializes in credential theft and intelligence collection and is linked to a handful of threat groups like APT 28 and Fancy Bear. The GRU GTsST uses cyberoperations to disrupt foreign infrastructure. It’s linked to several major disruptions including the 2017 NotPetya attack. This is where we find Sandworm.
What's in a name?
Nation-state threat group names do not always refer to a branded group of operators. There is no ‘Sandworm department’ in the GRU, nor is Sandworm activity normally found in threat intelligence feeds. The threat group is the GRU GTsST, and ‘Sandworm’ describes the threat activity conducted by its members, as observed by researchers. The industry treats these like group names to clarify attribution and simplify tracking. You may see Sandworm and its aliases referred to as groups or campaigns.
The name Sandworm was assigned by analysts at iSIGHT Partners (now part of Mandiant) who were studying the 2014 BlackEnergy attacks mentioned at the start of this post. While digging through the BlackEnergy malware binaries, they found references to arrakis02, houseatreides94, BasharoftheSardaukars, SalusaSecundus2, and epsiloneridani0. These terms appeared to be derived from the fictional world of Frank Herbert’s Dune. ESET researchers independently found the same references in a variant of BlackEnergy around the same time. The name Sandworm was widely adopted over the next few years.
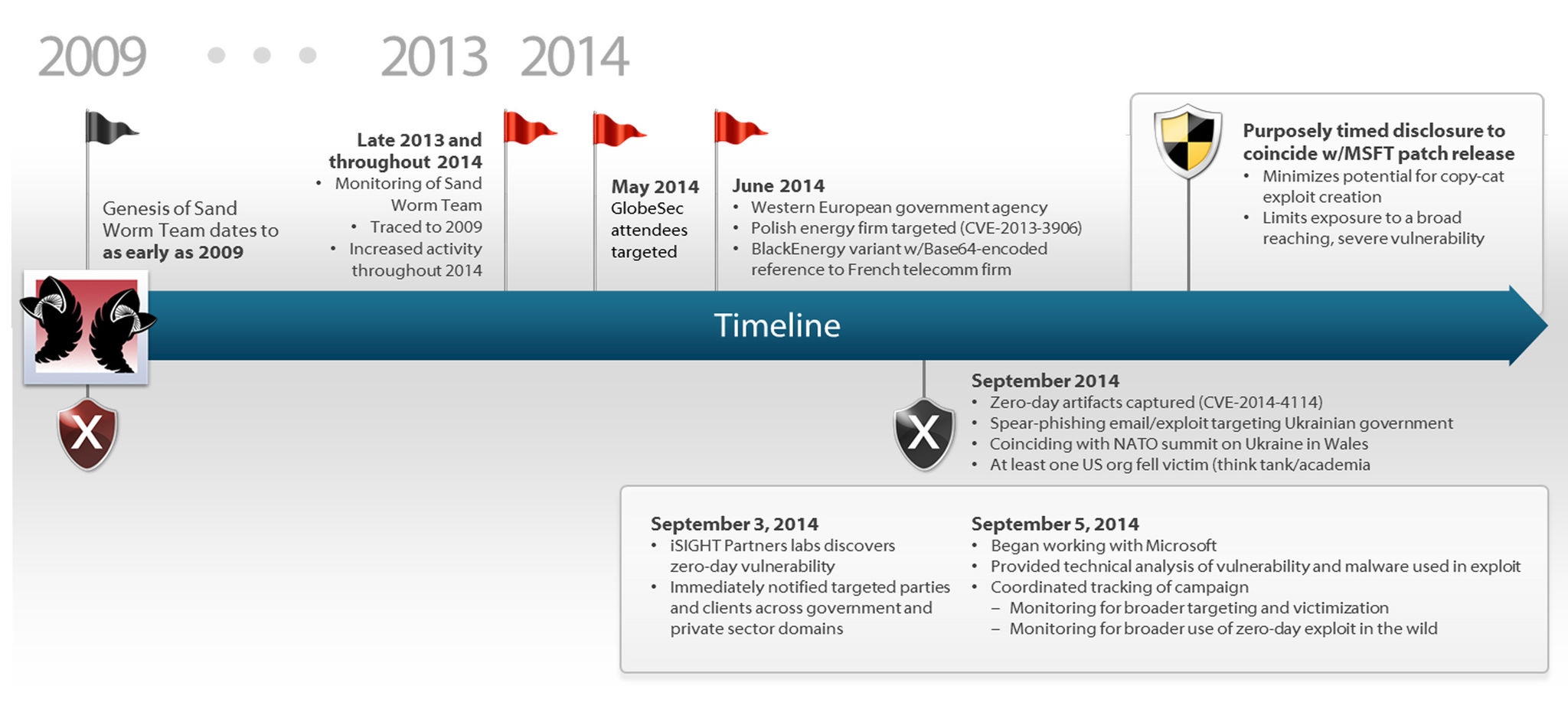
Sandworm timeline 2009-2014, via iSight Partners in collaboration with Microsoft
Sandworm’s operations evolved and expanded over the years, and security researchers created new names to describe these changes. The group has several aliases, including Voodoo Bear (Crowdstrike), IRON VIKING (Symantec), Seashell Blizzard (Microsoft), and APT44 (Mandiant).
The Sandworm actors do not seem to care what we call them, and they don’t mind being seen as long as they can establish plausible deniability for the state. When the group is getting too much attention it hides behind hacktivist groups like CyberArmyofRussia_Reborn (CARR), XakNet Team, Infoccentr, Killnet, Solntsepek, NoName057(16), Z-Pentest and Sector 16. Some of these groups appear to have direct links and close collaboration with the GRU, while others appear to be independent of the state but aligned with its goals.
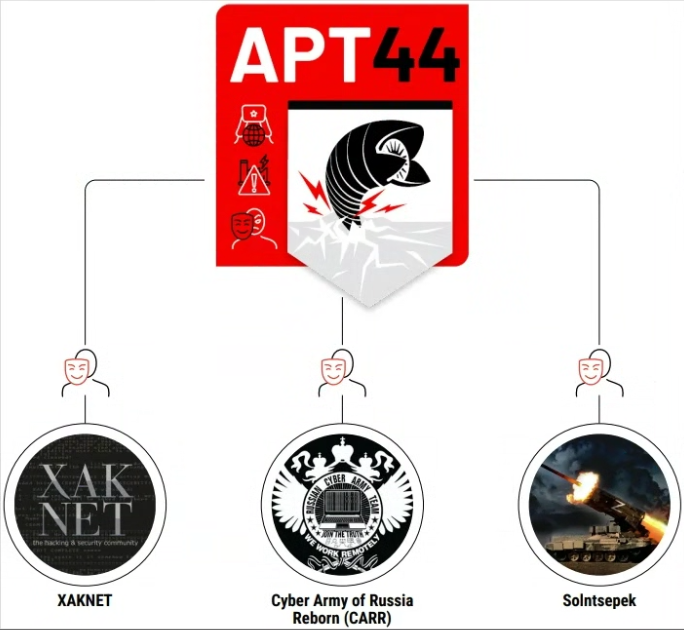
Top three hacktivist-branded Telegram channels linked to Sandworm, via Mandiant research
You can find more on these relationships here:
- Hacktivists Collaborate with GRU-sponsored APT28 (Updated with APT44 information) | Mandiant
- APT44: Unearthing Sandworm | Mandiant
- Pro-Russia Hacktivists Conduct Opportunistic Attacks Against US and Global Critical Infrastructure | CISA
Location and identities
The GRU and Sandworm operators are military intelligence officers acting on assignment. They are headquartered in Moscow, though individuals may be deployed as needed.
Attribution to the GRU is based on technical indicators of malware families and infrastructure, as well as its strategic and tactical alignment with Russian objectives. Further evidence is found in a 2020 federal indictment charging six named GRU Unit 74455 officers with conspiracy to conduct computer fraud and other offenses related to Several high-profile attacks.
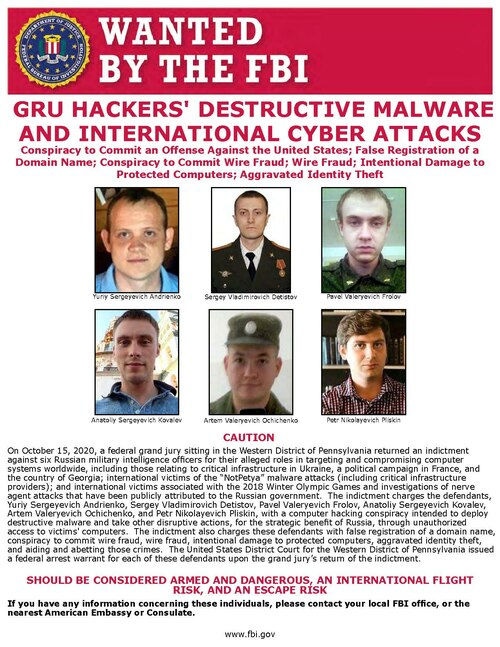
None of these suspects are known to be in custody. The text of the indictment has more details on operations of GRU and attribution to the Russian Federation and the key points are summarized here.
History and notable attacks
The earliest detectable activity attributed to Sandworm dates to approximately 2009, when the group conducted stealthy espionage operations targeting government and energy organizations in Ukraine and Eastern Europe. The attackers used early versions of BlackEnergy, a toolkit also used by other Russian-aligned threat actors, which made attribution difficult at the time. The group was hyper-focused on stealth, and these early intrusions were rarely noticed by the wider security community. Sandworm behaved primarily like a traditional espionage group focused on regional intelligence collection through 2014.
On December 23, 2015, Sandworm carried out the world’s first confirmed malware-induced power outage, compromising Ukrainian power distribution companies using BlackEnergy3 delivered through spear-phishing months earlier. Attackers remotely operated power grid control systems and deployed KillDisk to slow recovery efforts, leaving roughly 230,000 customers without electricity for several hours.
The following year, Sandworm demonstrated even greater sophistication with the deployment of Industroyer, a modular malware platform designed to communicate directly with industrial control protocols. This capability to interact directly with power grid equipment placed Sandworm among the most advanced cyber operators ever observed.
The group’s most infamous operation came in 2017 with NotPetya, which spread globally after attackers compromised the update mechanism of the Ukrainian accounting software M.E.Doc. Although it appeared to be ransomware, the malware irreversibly destroyed data and spread rapidly through corporate networks using the EternalBlue SMB exploit and credential theft techniques. Major global companies experienced catastrophic operational disruption, though they were not the targets of the attack. The costs of global damages were estimated to be over $10 billion, making NotPetya the most costly cyberattack ever recorded.
In 2024, Mandiant formally reclassified the group as APT44, consolidating Sandworm and related activity clusters into a single long-running threat actor.
Sandworm’s early history explains how the group was able to create physical-world consequences from a cyberattack. The operations below represent Sandworm's most operationally relevant known attacks, from the most recent backward:
- January 2026 —Microsoft and Amazon reported sustained targeting of Western critical infrastructure, via misconfigured network edge devices, VPNs, and collaboration platforms across North America and Europe.
- 2024–2025 — A newly identified wiper named ZeroLot is deployed against Ukrainian energy companies. The wiper is identified as purpose-built destructive tooling developed by Sandworm.
- 2023 — Sandworm deploys Infamous Chisel, a malware campaign targeting Android devices used by the Ukrainian military.
- April 2022 — Defenders stopped an attempted attack against a Ukrainian energy substation. Analysis of the attack found a retooled version of the 2016 Industroyer malware, paired with CaddyWiper and multiple Linux wipers deployed via Group Policy.
- February 2022 —At the start of the Russia-Ukraine war, Sandworm deployed multiple destructive wipers against Ukrainian government and commercial targets to degrade communications and infrastructure ahead of ground operations.
- Late 2021–2022 — Sandworm establishes persistent footholds in WatchGuard and ASUS network devices with Cyclops Blink.
- October 2022 — RansomBoggs and Prestige ransomware are deployed against organizations providing humanitarian or military aid in Ukraine and Poland. These ransomware variants were aimed at destruction rather than financial gain, like the 2017 NotPetya attack.
- October 2019 —Widespread defacement and denial-of-service attacks against Georgian government and media websites are used to signal political pressure.
- February 2018 —Olympic Destroyer is launched against the PyeongChang Winter Olympics, taking down IT services, TV broadcast feeds, and credentialing systems in the days before the opening ceremony.
Taken together, these operations illustrate the steady escalation of Sandworm’s capabilities and mission. Sandworm’s activity has aligned closely with Russian military objectives, particularly during its war with Ukraine. Disk wipers, satellite network disruptions and repeated attempts to interfere with energy and transportation infrastructure align with Russian military operations against Ukraine.
Defend yourself
Implementing a defense against Sandworm (APT44) requires a tiered strategy that addresses their shift toward edge device exploitation and "Living-off-the-Land" (LotL) tactics. Because this group prioritizes physical sabotage and widespread data destruction, perimeter-focused controls must be supplemented with robust internal segmentation and recovery planning.
The following recommendations are prioritized by their current primary attack vectors:
- Edge hardening (Critical): Inventory and patch all internet-facing systems—specifically VPNs, firewalls, and mail servers—within 24–48 hours of exploit disclosure.
- Identity & access management: Enforce phishing-resistant multifactor authentication (MFA) on all administrative and remote access interfaces. Monitor for the unauthorized use of native tools like PsExec or certutil.exe, which the group uses to move laterally.
- IT/OT segmentation: Strictly isolate enterprise IT from industrial environments with no direct internet access from control networks.
- Wiper-ready backups (Critical): Maintain immutable, offline backups. Sandworm is known to target and erase mapped drives and live backup infrastructure during the attack phase.
- OT-specific monitoring: Deploy behavioral monitoring to detect unusual industrial protocol activity.
- Proactive threat hunting: Search for behavioral red flags, such as the unexpected installation of remote monitoring and management (RMM) tools or Tor-related traffic from endpoints.
You can find more detailed information here:
- Sandworm Team MITRE ATT&CK
- Russian Military Cyber Actors Target US and Global Critical Infrastructure
BarracudaONE
Maximize your protection and cyber resilience with the BarracudaONE AI-powered cybersecurity platform. The platform protects your email, data, applications, and networks, and is strengthened by a 24/7 managed XDR service, unifying your security defenses and providing deep, intelligent threat detection and response. Manage your organization’s security posture with confidence, leveraging advanced protection, real-time analytics and proactive response capabilities. Robust reporting tools provide clear, actionable insights, helping you monitor risks, measure ROI and demonstrate operational impact. Don’t miss the opportunity to get a demo of the platform from our cybersecurity experts.

Rapporto sulle violazioni della sicurezza e-mail 2025
Risultati chiave sull'esperienza e l'impatto delle violazioni della sicurezza e-mail sulle organizzazioni a livello mondiale
Iscriviti al blog di Barracuda.
Iscriviti per ricevere i Threat Spotlight, commenti del settore e altro ancora.
The MSP Customer Insight Report 2025
Uno sguardo globale su ciò di cui le organizzazioni hanno bisogno e vogliono dai loro provider di servizi gestiti per la sicurezza informatica