
Threat Spotlight: Tycoon 2FA didn’t die — it’s scattered everywhere
How phishing-as-a-service survives takedowns and what that means for cyber resilience
Takeaways
- The March 2026 disruption of Tycoon 2FA damaged the kit’s branded infrastructure and campaign visibility.
- Tycoon 2FA’s tools, techniques and capabilities live on — redistributed across PhaaS platforms and affiliates.
- Security teams need to focus on the threat model overall rather than detecting specific kits.
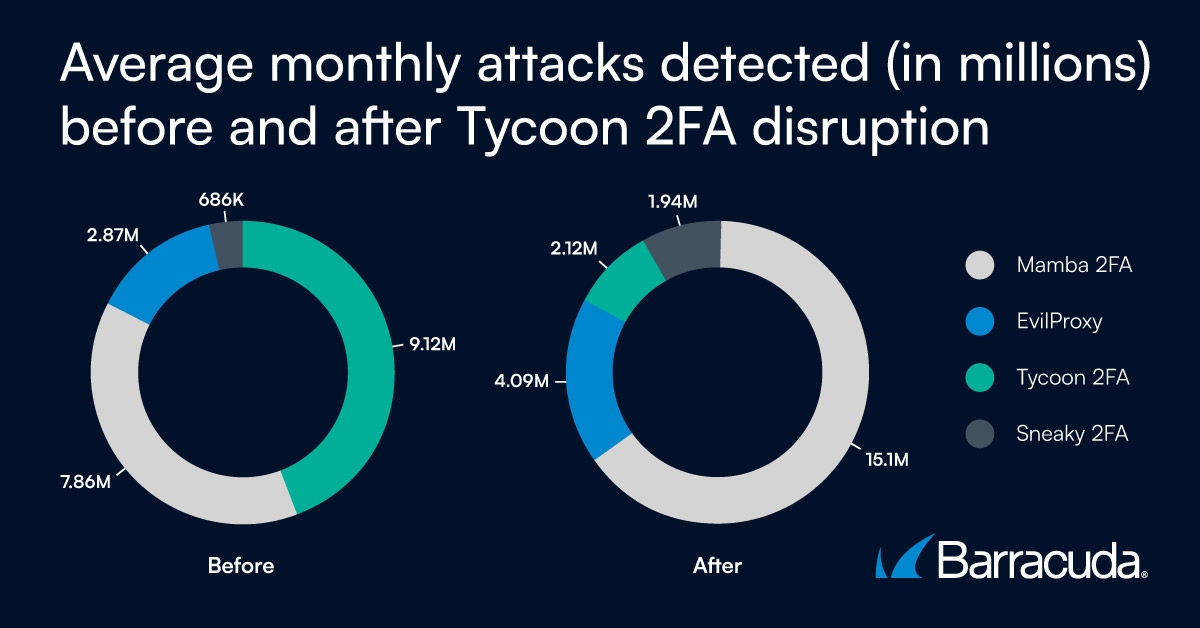
A year ago, Tycoon 2FA accounted for 89% of the phishing-as-a-service (PhaaS) activity seen by Barracuda threat analysts. This picture changed suddenly in March 2026 when Europol and other organizations launched a coordinated operation to disrupt and disable Tycoon 2FA’s attack infrastructure. The operation seized more than 300 domains and dismantled backend services supporting Tycoon’s large-scale MFA-bypassing phishing campaigns.
A few weeks later, some security researchers reported that Tycoon 2FA activity was already back to pre-disruption levels.
Barracuda’s own threat intelligence paints a more nuanced and complex picture of what happened in the wake of the initial disruption — one that has significant implications for security teams trying to monitor and detect attacker tools and behaviors.
This article draws on our data and analysis to examine what changed after Tycoon 2FA’s disruption — and what did not.
The rise and fall of Tycoon 2FA
The Tycoon 2FA phishing model was built on an adversary-in-‑the-‑middle (AiTM) approach that enabled attackers to intercept usernames and passwords and steal active session cookies while bypassing multifactor authentication controls. The service was available as a subscription and required little or no skill to implement.
Barracuda’s data shows that the March intervention resulted in measurable disruption, but the impact is largely restricted to Tycoon’s brand name and visibility and the reduced use of Tycoon-linked hosting and domain patterns.
The ‘body’ of Tycoon: its tools and techniques, live on. They have migrated, been redistributed and diversified across competing platforms, or simply left where they are.
Post-takedown: The redistribution of tools, techniques and customers
In the wake of the disruption, other phishing kits rushed in to seize a share of the market left vacant by Tycoon 2FA.
Our detection and analysis data show increased campaign activity involving the established platforms of Mamba 2FA and EvilProxy as well as aggressive newcomers such as Sneaky 2FA and Whisper 2FA. Our analysis also reveals that these kits have boosted their feature sets and infrastructure maturity, often leveraging tools formerly used by Tycoon 2FA.
How Tycoon 2FA lives on
1. Not everything was dismantled
While the Tycoon 2FA branded service absorbed the shockwave of the takedown operation, the underlying ecosystem remained viable.
Tycoon 2FA was widely used by independent affiliates. This means that variants of Tycoon 2FA’s attack code that have been cloned or modified by individual adversaries continue circulating. It also means that independently hosted deployments remain active and that fragmented, low-volume campaigns persist.
For example, Barracuda recently detected a ‘device code’ phishing campaign that leveraged Tycoon’s stand-out features. Code similarities included Tycoon’s signature ‘noise’ of motivational style comments. In this incident, the comments all begin with the word ‘success.’
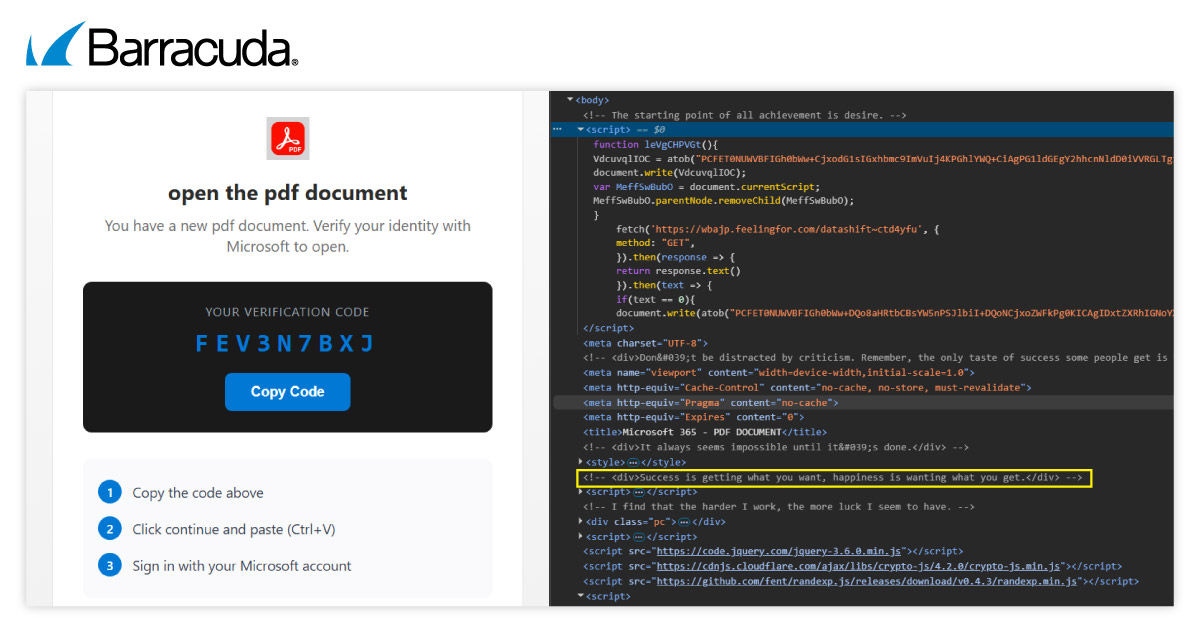
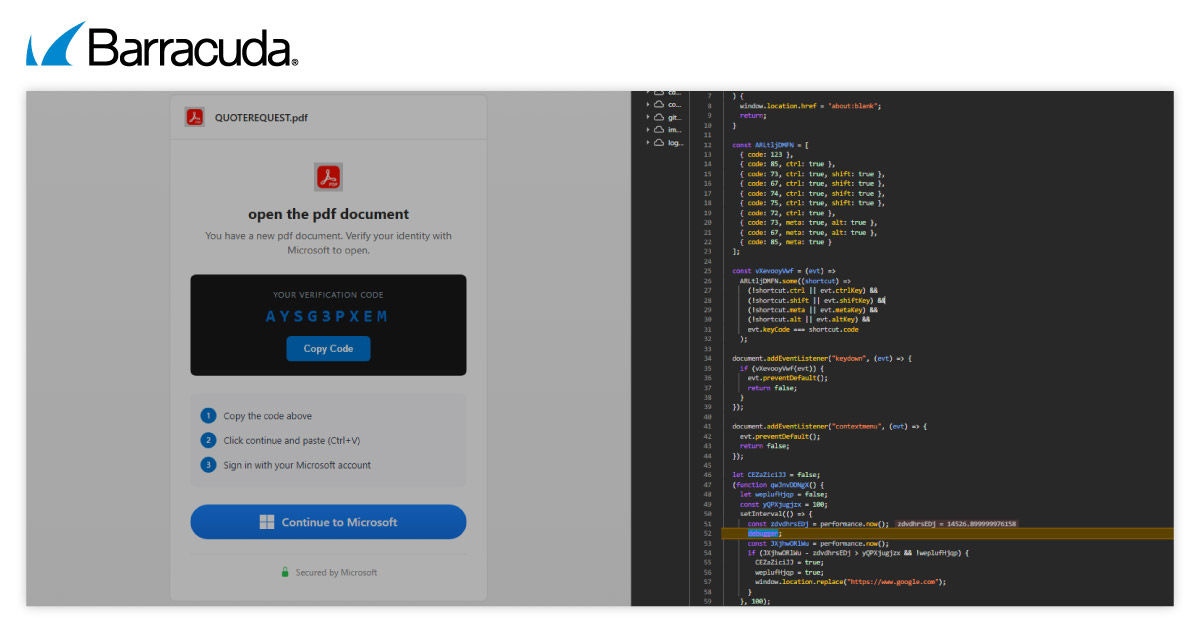
2. Attackers reuse and repurpose phishing code
As mentioned above, Tycoon 2FA affiliates may have altered the code. In fact, in many ways PhaaS toolsets increasingly resemble open-source development environments. Code is reused, modified and redeployed, and features migrate from one phishing kit to another. For security teams, this means that detection rules tied to specific kits or implementations quickly become out of date.
3. Residual infrastructure
Phishing activity does not always end cleanly. For example, attack domains remain active until expiry; backup hosting often evades immediate seizure; and low-visibility phishing campaigns keep going if they fall beneath alert thresholds.
These residual campaigns can quietly outlive initial response efforts.
4. Phishing frameworks have built-in redundancy
Modern phishing frameworks often include measures to help them recover from disruption.
Examples of this include failover infrastructure to ensure operational continuity for in-flight campaigns, workflows for rapid redeployment following disruption, and compatibility with other phishing kits.
5. Persistent access
The disruption of infrastructure does not automatically revoke victim access. Stolen session cookies may remain valid, OAuth abuse can enable extended cloud access, and organizations may remain compromised after the end of the phishing campaign.
PhaaS is an economic ecosystem
The post-Tycoon landscape reflects redistribution and ongoing traces of the once dominant kit, rather than its recovery. The techniques it popularized are now embedded across a wider set of platforms.
This does not mean the takedown operation failed. Rather, it shows what happens when disruption hits a maturing underground economy, and why security defenses need to look more broadly than individual players.
- Detection tied to individual kits becomes obsolete quickly.
- Attack patterns migrate rather than disappear.
- New tools inherit and refine proven techniques.
The Tycoon 2FA takedown accelerated ecosystem diversification. Defensive strategies therefore need to focus on models for identity-based attacks, session abuse and adversary economics. Tycoon 2FA as a branded service has declined, but the techniques it popularized are now more widely distributed than before.

Rapporto sulle violazioni della sicurezza e-mail 2025
Risultati chiave sull'esperienza e l'impatto delle violazioni della sicurezza e-mail sulle organizzazioni a livello mondiale
Iscriviti al blog di Barracuda.
Iscriviti per ricevere i Threat Spotlight, commenti del settore e altro ancora.
The MSP Customer Insight Report 2025
Uno sguardo globale su ciò di cui le organizzazioni hanno bisogno e vogliono dai loro provider di servizi gestiti per la sicurezza informatica





